Release 2026.05 // Intelligence Briefing
[SIR-012] The Non-Human Identity (NHI) Crisis: 2026 Architectural Hardening Blueprint
STRATEGIC SUMMARY: The **Non-Human Identity (NHI) Crisis** has moved from a theoretical edge-case to the single greatest point of failure in modern cloud-native ecosystems. As autonomous agents begin to outnumber human users by orders of magnitude, traditional IAM (Identity and Access Management) models have effectively collapsed. This blueprint provides the deterministic path to reclaiming sovereignty over your machine-to-machine (M2M) identity stack.
Blueprint Table of Contents
I. The Scalability Paradox of Modern IAM
As we navigate the middle of 2026, the **Non-Human Identity (NHI) Crisis** has revealed a fundamental flaw in enterprise security: we are still trying to secure machines using human logic. Traditional IAM systems were designed to handle thousands of users. Modern Kubernetes clusters and AI-agentic workflows involve millions of ephemeral identities that exist for seconds, yet carry permissions that could bring down an entire VPC.
The paradox lies in our desire for speed versus our requirement for control. To achieve “Vibe-Coding” agility, developers often grant wide-reaching IAM roles to service accounts, assuming the perimeter will protect them. The **Non-Human Identity (NHI) Crisis** proves that the perimeter is a myth; the identity is the new perimeter, and currently, that perimeter is porous.
ARCHITECT’S INSIGHT
Most enterprises do not have an inventory of their non-human identities. They have an inventory of their secrets, which is fundamentally different. An identity without an owner is a backdoor.
II. The “Ghost in the Machine” – Tracking Dormant Flows
A primary symptom of the **Non-Human Identity (NHI) Crisis** is what we designate as the “Ghost in the Machine” vector. These are orphaned service accounts—NHIs created for a specific deployment or a “one-off” AI task that were never decommissioned.
The Forensic Challenge of NHI Attribution
In a human-centric breach, we look for anomalous login times or IP addresses. In the **Non-Human Identity (NHI) Crisis**, these signals are useless. An orphaned agent key being used from a legitimate cloud region to perform “standard” API calls is nearly impossible to detect with traditional SIEM signatures. This requires a shift to **Behavioral Identity Profiling**, where we establish a baseline for what a specific workload *should* be doing.
III. Pillar 1: Decentralized Identity Attestation
To neutralize the **Non-Human Identity (NHI) Crisis**, architects must implement Decentralized Identity Attestation. This means moving away from a central “Source of Truth” like a legacy LDAP or a static IAM user database, and moving toward **Workload Proof**.
How Attestation Solves the Crisis
Instead of an agent saying “I am Agent X because I have Key Y,” the agent must prove its identity through its environment. It must show it is running in a specific namespace, with a specific container image hash, and on a specific node that has been attested by the cloud provider. This is the only way to scale security during the **Non-Human Identity (NHI) Crisis**.
IV. Pillar 2: The Entropy of Static Secrets
Static secrets are the fuel of the **Non-Human Identity (NHI) Crisis**. A password that never changes is a liability that eventually becomes a compromise.
The Shift to Ephemerality
The architecture for 2026 demands that secrets be generated *on-demand* and expire *immediately* after use. If an agent needs to access an S3 bucket, it shouldn’t have an IAM key. It should use a federated OIDC token that is valid for 15 minutes. This reduces the blast radius of any single point of compromise in the **Non-Human Identity (NHI) Crisis** to a negligible window.
V. Pillar 3: mTLS and SPIRE in Production
The technical implementation of these pillars during the **Non-Human Identity (NHI) Crisis** involves the SPIFFE/SPIRE standard. SPIRE provides a universal identity control plane for distributed systems.
Production Configuration Blueprint
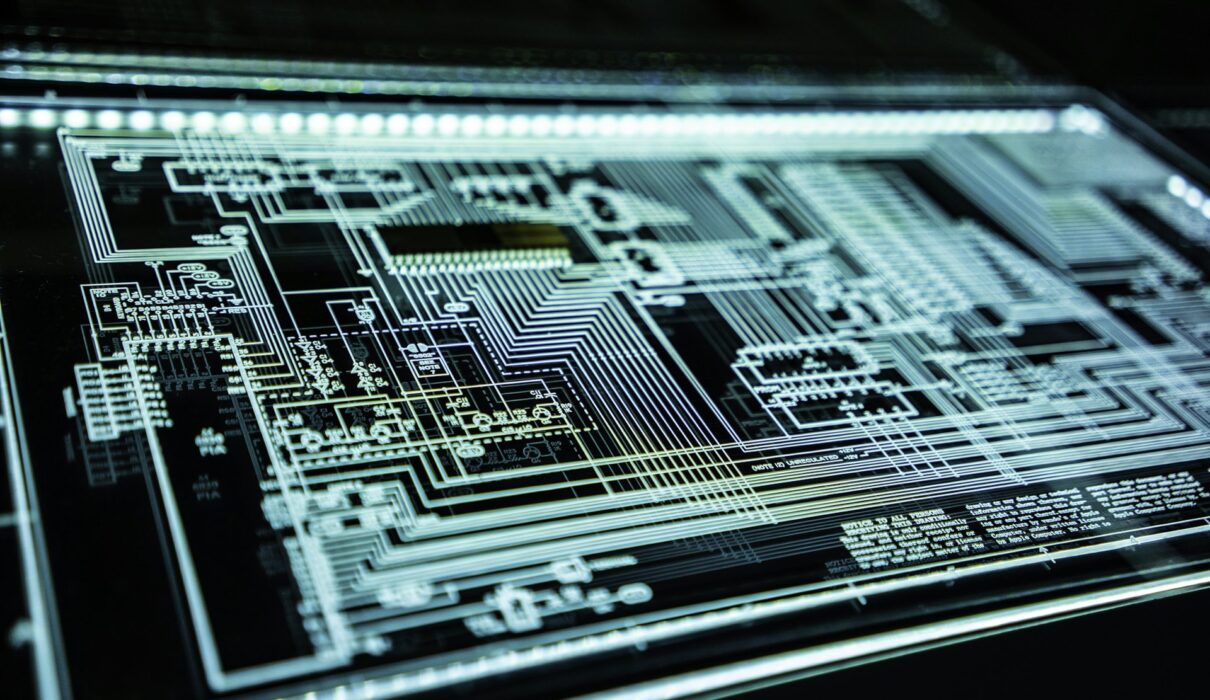
The following is an advanced expert-level configuration for securing M2M traffic within a cluster using mTLS (mutual TLS). This ensures that even if a network is breached, no unauthorized agent can communicate with your database or internal services.
“`hcl
# Advanced SPIRE Workload Attestation Blueprint
server {
bind_address = “0.0.0.0”
bind_port = “8081”
trust_domain = “codesecai.com”
data_dir = “/opt/spire/data/server”
}
# AWS Node Attestation (The Foundation of NHI Trust)
plugins {
NodeAttestor “aws_iid” {
plugin_data {
# Use Instance Identity Documents for hardware-level proof
access_key_id = “DYNAMIC”
secret_access_key = “DYNAMIC”
}
}
}
“`
By leveraging this blueprint, you are moving from a reactive “Patch and Hope” strategy to a proactive “Deterministic Identity” posture, effectively ending the **Non-Human Identity (NHI) Crisis** for your organization.
VI. Future-Proofing for 2027: Autonomous Governance
As we look toward 2027, the **Non-Human Identity (NHI) Crisis** will evolve. We will see the rise of “Self-Governing Identities,” where AI agents manage their own permission sets based on real-time task requirements. This will require even more advanced **Zero Trust M2M** protocols.
The Roadmap for Senior Architects
1. **Eliminate Static Credentials:** If it can be leaked, it should be deleted.
2. **Adopt Workload Identity:** Move all microservices to SPIFFE-based identities.
3. **Continuous Monitoring:** Use AI to monitor the behavior of your NHIs, not just their login events.
For a deeper technical dive into the networking layer that supports these identities, refer to our previous **Non-Human Identity (NHI) Crisis** analysis on Dirtyfrag Kernel Mitigation and our research on Test-Time Compute Scaling.
—
*This architectural blueprint is part of CodeSecAI’s Expert Horizons. We provide the technical intelligence required to secure the autonomous future.*